Managed Backup & Business Continuity
Wekos manages your entire backup stack — server backup, Microsoft 365 protection, and DR infrastructure — so that when something goes wrong, recovery follows a documented procedure executed by our engineers. Not a scramble.
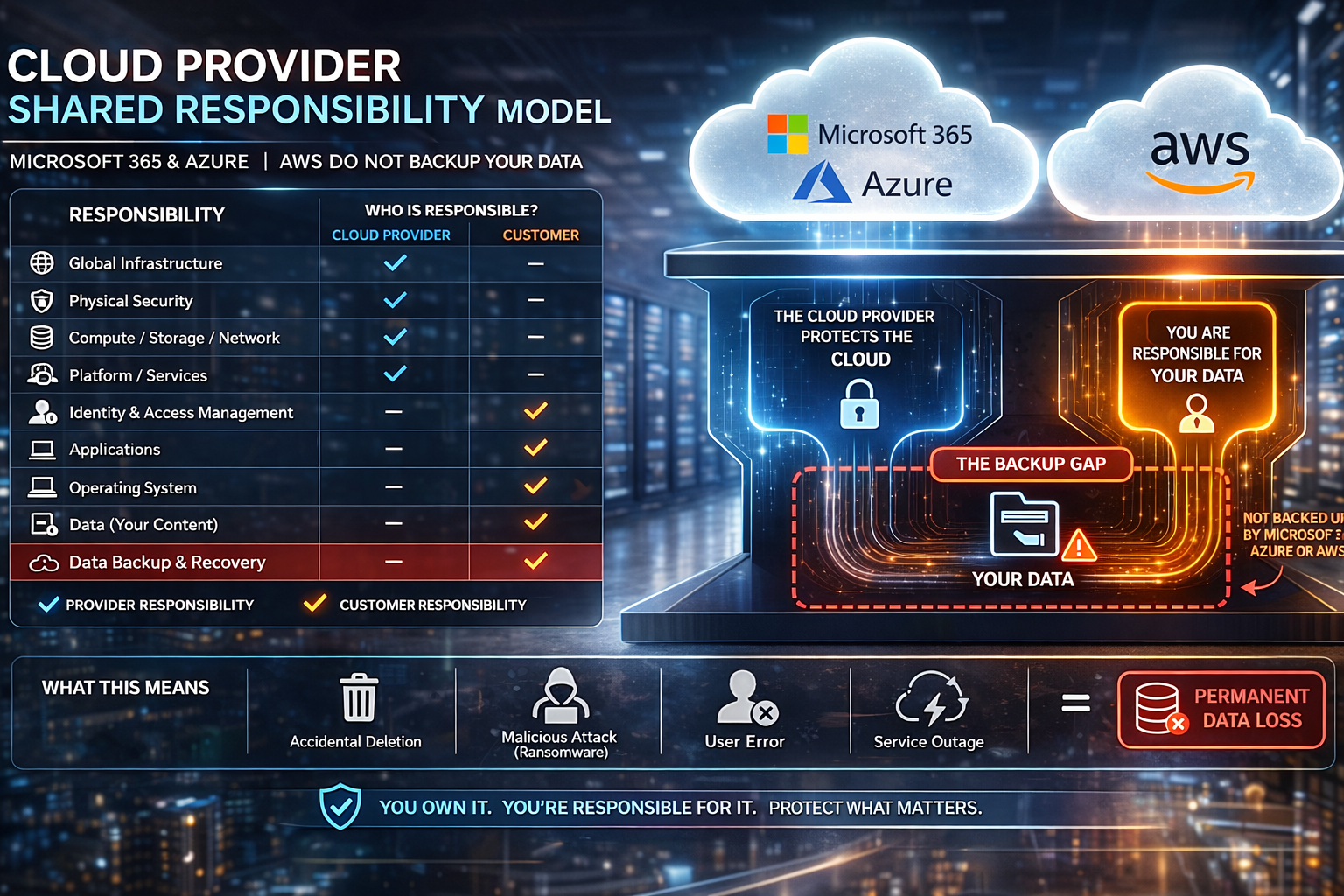
Your Cloud Provider Is Not Your Backup Provider
One of the most dangerous assumptions in IT is that because your data lives in the cloud, it is automatically protected. It is not. Microsoft, Google, Amazon, and every other major cloud provider operate under a shared responsibility model — they are responsible for the availability and resilience of their infrastructure, but the protection of your data is explicitly your responsibility.
Microsoft 365 retains deleted items for a limited window and provides basic version history — but it does not provide a true backup. If ransomware encrypts your SharePoint, if a malicious insider deletes your OneDrive, or if a misconfigured sync wipes your Teams data, Microsoft’s native retention may not save you. The same principle applies to Azure, AWS, and Google Workspace. Cloud storage is not cloud backup.
- Microsoft 365 has no native backup — it has retention policies with hard limits
- Deleted data beyond the retention window is permanently gone
- Ransomware that encrypts cloud-synced files propagates directly to OneDrive and SharePoint
- Azure and AWS storage replication protects against hardware failure — not against deletion, corruption, or ransomware
- Google Workspace Vault is an archive tool — not a backup and recovery platform
Ransomware Does Not Stop at Your Perimeter — And Neither Should Your Backup
Modern ransomware and cryptolockers are specifically designed to find and encrypt backup data before triggering the visible attack. They look for network shares, cloud-synced folders, connected backup drives, and accessible storage targets — and they encrypt those first. If your backup destination is reachable from an infected machine, your backups are not safe.
Wekos addresses this with a layered backup architecture that includes air-gapped storage, immutable backup copies, and offsite replication to Wekos-managed infrastructure that your production environment cannot reach. Immutable backups cannot be modified, encrypted, or deleted — not by ransomware, not by a compromised admin account, and not by mistake.

How Wekos protects your backups from ransomware:
- Immutable backup storage — copies that cannot be altered or deleted for a defined retention period
- Air-gapped offsite replication to Wekos infrastructure — unreachable from your production network
- Wasabi object storage with Object Lock for WORM-compliant retention
- Pre-restore malware scanning — workloads are tested in isolation before being brought back into production
- Microsoft 365 backup with independent retention — separate from Microsoft's own systems and limits
- Backup job monitoring with anomaly detection — unusual job behavior flagged before it becomes a problem
What's Included in Managed Backup & Continuity
This is an ongoing managed service — not a one-time setup. Wekos monitors your backup jobs daily, verifies restores on a regular schedule, manages your DR infrastructure, and maintains the documentation. You get protection that actually works, from engineers who are accountable for it.
What We Manage For You
Server Backup
- Managed backup for physical and virtual servers
- Daily job monitoring and failure alerting
- Tested restore procedures on a defined schedule
- Supports Veeam, Windows Server Backup, and agent-based solutions
- Retention policies configured to your compliance requirements
Microsoft 365 Data Protection
- Per-user backup of Exchange Online, SharePoint, OneDrive, and Teams
- Protects against accidental deletion, ransomware, and Microsoft retention gaps
- Granular restore — individual emails, files, or full mailboxes
- Retention configurable beyond Microsoft’s native limits
- Managed and monitored by Wekos — not a self-service portal
DR Infrastructure — Retainer
- Reserved DR capacity maintained at Wekos facilities
- Your environment spun up on demand when disaster occurs
- Fraction of the cost of always-on DR
- Defined activation process with documented runbook
- Suitable for businesses that can tolerate 2–4 hour RTO
DR Infrastructure — Active
- Fully active, continuously replicated DR environment
- Near-zero RTO for organizations that cannot tolerate downtime
- Veeam replication from on-premises to Wekos cloud infrastructure
- Regular replication health monitoring included
- Automatic failover capable with defined runbook
Backup Storage
- Scalable managed backup storage billed per GB
- No overprovisioning, no wasted capacity
- Offsite replication included for 3-2-1 compliance
- Wasabi object storage available for cold-tier retention
- Air-gapped and immutable options for ransomware protection
93%
of most ransomware attacks specifically target backup repositories before triggering encryption
0 days
Your call
Immutability is optional — but the businesses that wish they had it only find out after an attack
Choose Your Recovery Profile
Backing up your data is great for recovering an accidently deleted file. But what do you do when your infrastructure is gone due to a disaster or cyber event? You need some place to restore to. Most clients start with Standard protection and add DR infrastructure as their recovery requirements become clearer. All tiers include Wekos management, monitoring, and tested restore procedures.
Standard
Best for most SMBs focused on data loss protection.
- Server Backup + M365 Protection
- Daily monitoring and job verification
- Tested restore procedures
- Target RTO: Hours to days
DR Retainer
For businesses needing site-level recovery within hours.
- Everything in Standard
- Warm DR Infrastructure at Wekos
- Defined activation runbook
- Target RTO: 2–4 hours
DR Active
For organizations that cannot tolerate extended downtime.
- Everything in DR Retainer
- Hot Veeam replication
- Continuous replication monitoring
- Target RTO: Minutes
Need Enterprise-Grade DR Architecture?
The service tiers above describe what Wekos manages for you every day. If you’re evaluating a complex multi-site DR design, need to define formal RTO/RPO targets, or want to understand how Wekos approaches recovery architecture at the engineering level — our DR Expertise page covers that in detail.
